Along with an estimated 15,000 other people, the NSS Labs team spent last week living and breathing Black Hat 2017. This year marked the conference’s 20th anniversary, and for the most part, it was much the same as it has been in previous years: crowded and busy. (And tiring—I heard claims of over 17,000 steps being logged by more than one fellow attendee.) I did not sense an overarching theme this year, which was interesting to me. If I was pressed to provide one, I’d say it was data analytics; i.e., products that help you make sense of all your data.
There were great conversations with others in the security trenches; first-hand stories of varied challenges were swapped, and there was plenty of discussion about which security controls are working—and which are not. Endpoint security was a hot topic. Are you surprised at the number of new players in this space? Given that NSS reviewed more than 60 vendors last year, I know I am. It will be interesting to follow them and see how they differentiate themselves.
NSS has had a presence on the show floor for a few years now. This year, the NSS enterprise architecture research group (also known as the EARG) decided to poll visitors to the NSS booth on their security purchase priorities. The EARG prioritizes research topics that help the enterprise, and these topics extend beyond security effectiveness and performance.
Visitors were asked:
NSS Labs tests security products for security efficacy, performance, and value. Which of the following does your organization consider the next highest priority for a security purchase?
- Ease of Deployment
- Interoperability
- Manageability
- Vendor Technical Support
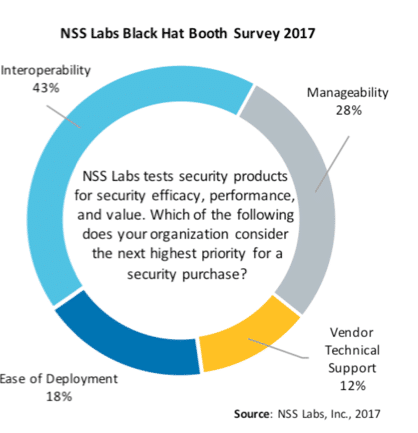
We collected more than 100 responses from participants representing 99 organizations, 15 countries, and IT security budgets that range from ~US$200K to over US$1B. Our survey revealed that after security effectiveness, performance, and value, interoperability is most frequently selected as a security purchase priority.
This focus on interoperability confirms our own thoughts and aligns with one of our research themes, which is the role of DevOps and SecOps teams in security control deployments, and a review of how efficiently security controls share data. A product’s ability to interoperate with other controls directly affects its total cost of ownership (TCO). Ultimately, enterprises that must spend time stitching together products with custom code incur hidden costs that may not be immediately apparent.
TCO calculations should always be a factor in security control purchasing decisions. NSS has long assessed this metric and is constantly evolving its definition. For example, where earlier versions of NSS’ TCO Comparative Reports focused primarily on hardware and maintenance costs, NSS’ Advanced Endpoint Protection TCO Comparative Report examines the true cost of responding to incidents, and the differences between products that block and products that detect.
Why do we go to Black Hat? Many security practitioners show up for the education and training opportunities, vendors attend for the sales opportunities, and the analysts are there for well, all of it. Regardless of your motive for attending, most agree that some of the best moments happen at the end of the day, when you’ve finished making the rounds on the show floor and you have a chance to relax with colleagues at happy hour. If I didn’t see you this year, I hope to catch up next time!
